A recent report by the Mineta Transportation Institute indicates that the demands outlined in cybersecurity-focused executive orders or EOs issued by President Biden may create “sourcing limitations” for transit operators trying to comply with them.
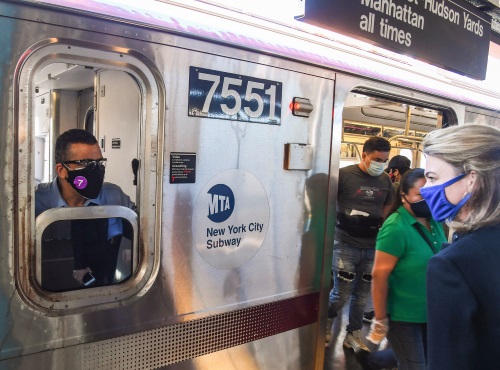
[Above photo by the Metropolitan Transportation Authority]
The MTI said the recent cyberattacks against the Bay Area Rapid Transit or BART system in San Francisco, Southeast Pennsylvania Transportation Authority, and Vancouver’s Translink, among others, puts into stark relief the cybersecurity needs of the transit industry.

Thus the group’s report – entitled Will the Biden Administration’s ‘Made in America’ Executive Order Present Significant New Cybersecurity Obligations for Transit Operators? – analyzes how the president’s recent EOs as well as new cybersecurity laws put in place over the past several years impact transit operators.
MTI recommends that transit providers and their respective vendors take into account the following findings from its report:
- The supply chain restrictions in multiple EOs suggest that U.S. transit agencies will likely need to find new sources for multiple products, including items purchased from or containing components produced by Huawei and other Chinese providers.
- More sourcing limitations are likely to reduce the number of acceptable vendors, potentially increasing the cost of goods.
- Transportation executives should educate themselves about the exemption processes associated with each of the EOs, the government agency staff leading the efforts (a resource for EO interpretation or clarification), and, when needed, take action to file an exemption request.
Cyberattacks based on security or software flaws are certainly common, but the easiest path for a cyber-attacker to follow is gaining physical access to a part of a desired system, MTI said.
As a result, EO 14005 – also known as the “Made in America” order – acknowledges that “significant risk” and mandates greater scrutiny of the origin of computer hardware and its associated supply chain.

MTI noted that a hostile nation or other “nefarious actor,” for example, could easily collaborate with a local manufacturer to create a sophisticated “back-door” that could be exploited to inflict significant damage in a product destined for the United States.
In addition, President Biden issued EO 14024 – entitled “Blocking Property with Respect to Specified Harmful Foreign Activities of the Government of the Russian Federation – in response to persistent Russian cyberattacks in April, followed by EO 14028 – Improving the Nation’s Cybersecurity – in May.
“The ‘Made in America’ EO and similar directives demonstrate a level of consistency in U.S. policy across party lines,” MTI explained in a statement. “This means that future policies aimed at making the U.S. supply chain more resilient are unlikely to deviate much from the current playbook,” the group added.
“Because America depends on its transportation infrastructure, transit will likely remain a prime target for nefarious actors seeking to disrupt communities,” it said. “As technology evolves to enable the industry’s goals, operators and experts must adapt and prepare for the risks today and in the years to come.”
 Nation
Nation